Understanding Military Kill Switches in Drones
Explore the critical role of military kill switches in drones. Learn how these advanced safety circuits protect mission data and ensure operational integrity under electronic warfare and cyber thre...
4/19/20261 min read
In SpearX, we get asked often: “Isn’t a 'Kill Switch' just a button to stop the motors of UAV?” In Civilian Drones, yes. In Military Systems, it is something completely different.
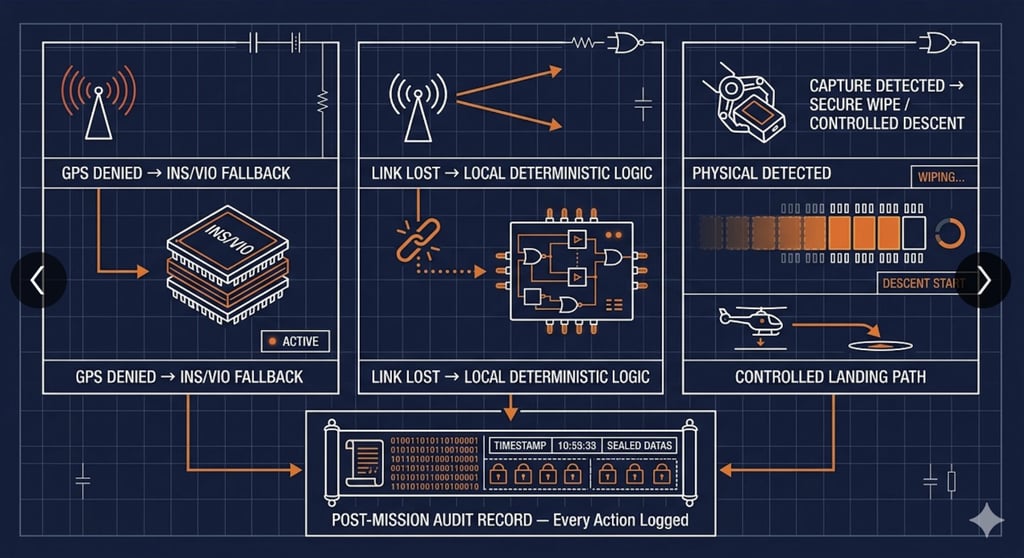
A military 'Kill Switch' is not a simple command. It is a trusted, hardware-isolated safety circuit designed to work under electronic warfare, cyber attacks, & physical capture. Its goal is not just to stop flight. It is to protect mission data, prevent technology leaks, and follow strict rules of engagement.
How do we build it at SpearX?
We use a layered approach:
- Level 0: Hardwired circuit.
A physical break in motor power. Works independently from software or operating systems.
- Level 1: Secure chip (TEE/HSM).
Runs on a real-time OS, stores encryption keys, and wipes data instantly if the casing is opened.
- Level 2: Protected command link.
Uses frequency hopping, strong encryption, and time-limited tokens. Commands must be verified before execution.
- Level 3: Deterministic logic.
Checks signal origin, mission state, and location. Local hardware always wins over AI or autopilot software.
Why does this matter for AI drones? Because autonomy must never override safety.
Our rule is clear: the hardware watchdog has higher priority than any neural network. If the system loses trust, it does not guess. It executes a controlled landing or secure data wipe, depending on the mission profile.
We also design for real combat conditions. GPS can be jammed. Radio links can be intercepted. Drones can be damaged or captured.
That is why our kill system does not rely on cloud services, uses inertial/visual navigation for fallback, & logs every action in a tamper-proof record for post-mission review.
Building these systems is not just about code.
It's about trust, verification, and engineering discipline.
Every logic path is tested under signal jamming, cyber stress & hardware failure. Because in defense, there is no “try again” button!
Related : GEOCOM Co. LLC www.geocomco.eu DeepTechRnD www.deeptechrnd.eu SpearXAgro www.spearxagro.eu
Contacts
SpearX ↑ Strike with Precision
+359 877 620 210
D-U-N-S® 525540791


© 2025 - 2026. All rights reserved. SpearX Projects. Geocom Co. LLC






SpearX is an EU-Ukrainian company located in a strategic areas for R&D in UAV
